Image hash processing method based on adjacent gradient and structural features
A technology of structural features and processing methods, applied in the field of image processing, can solve problems affecting image classification performance and weak robustness, and achieve low collision rate and high safety performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
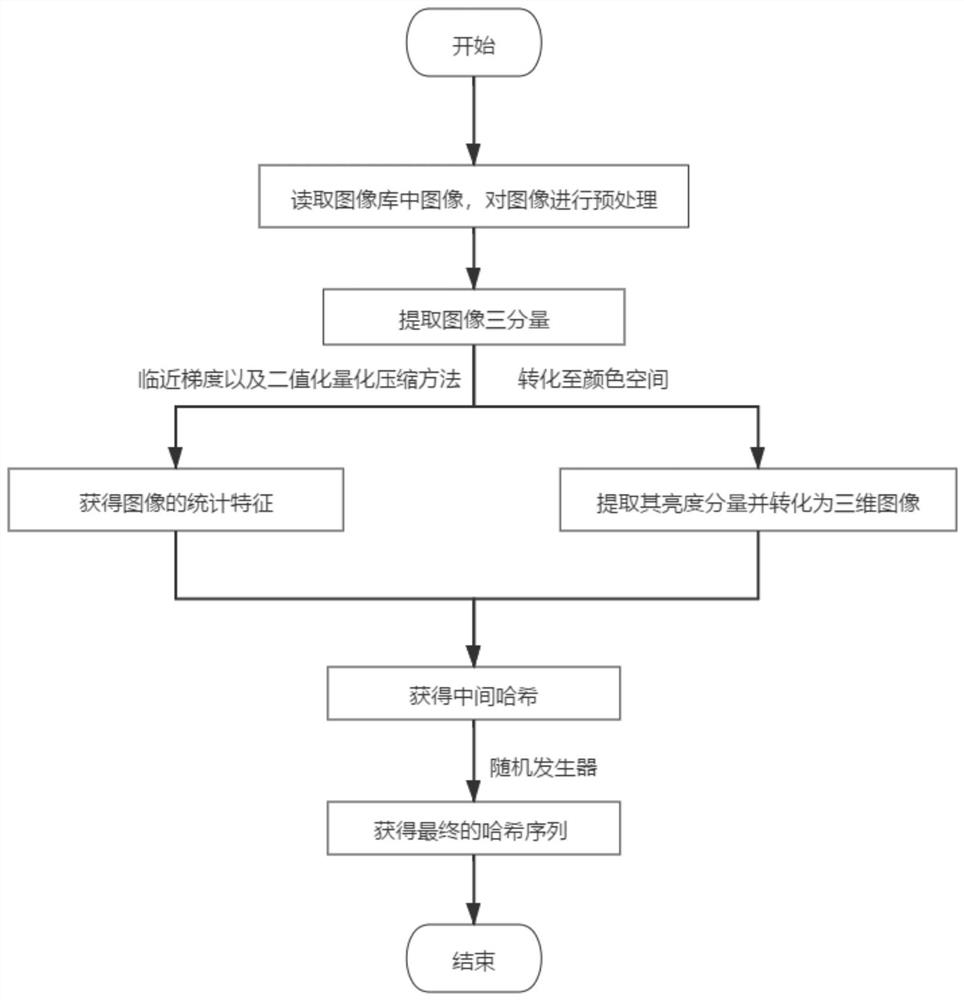
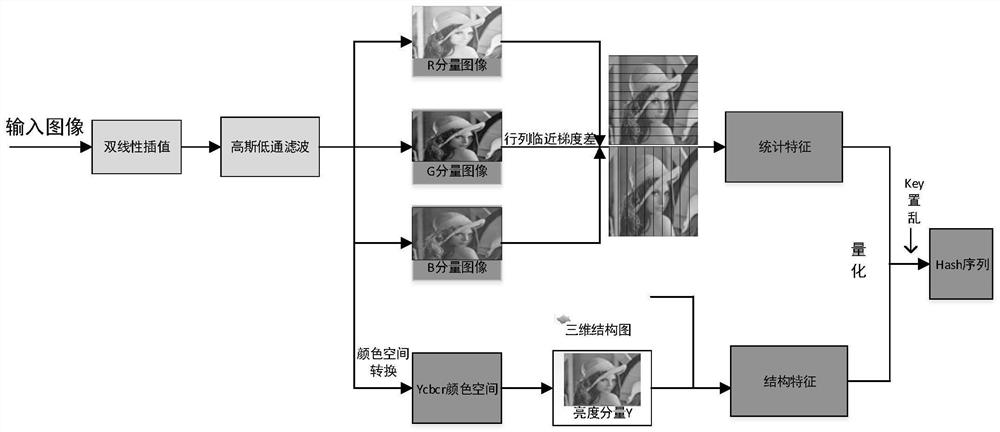
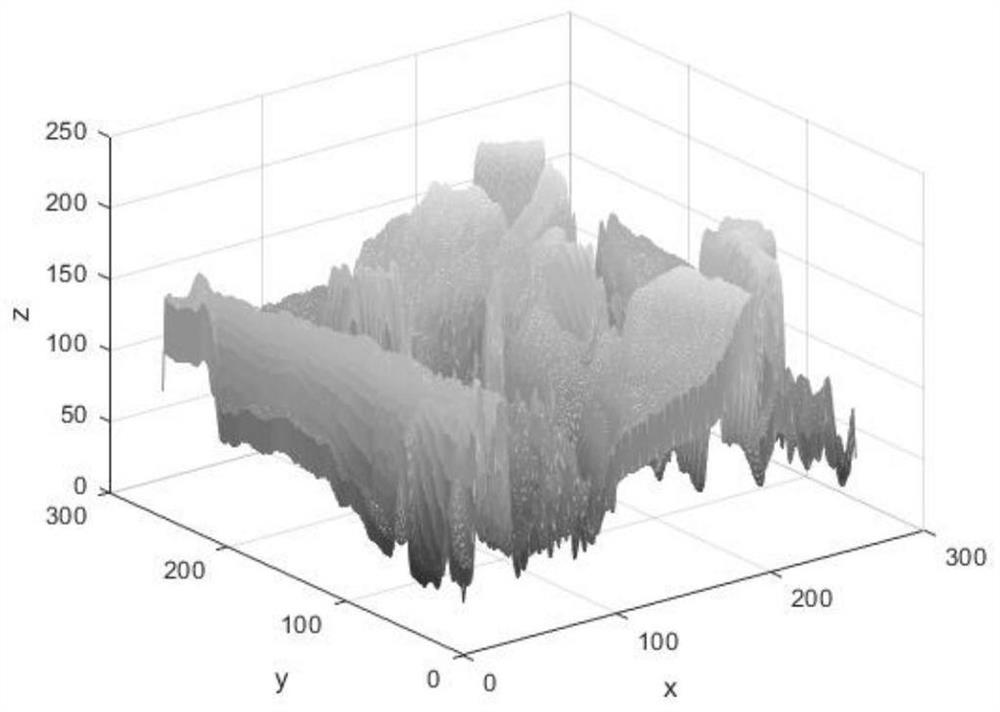
[0046] refer to Figure 1~4 , is an embodiment of the present invention, provides a kind of image hash processing method based on adjacent gradient and structure feature, comprises:
[0047] S1: Read the image in the image library, and preprocess the image. It should be noted that,
[0048] Preprocessing the image includes normalizing the image to the same size, and performing a Gaussian low-pass filtering operation after the image is resized to reduce noise pollution.
[0049] Gaussian low-pass filtering The filtering operation includes using a Gaussian low-pass filter with a template of 3×3 and a standard deviation σ of 1 to filter the image. The calculation formula of the filtering process is as follows:
[0050]
[0051]
[0052] Among them: M G (i, j) is the element value of row i and column j in the template.
[0053] S2: Extract the three components of the preprocessed image, and use the adjacent gradient and binarization quantization and compression methods to o
Embodiment 2
[0091] refer to Figure 5-8 It is another embodiment of the present invention, in order to verify the technical effect adopted in this method, and to verify the real effect of this method by means of scientific demonstration.
[0092] When conducting experiments, first set the parameters as follows: image normalization size N=256, 3×3 Gaussian low-pass filter, standard deviation is 1, image sub-block size b=8, thus hash length L=L 1 +L 2 =12×N / b-2=382 bits.
[0093] First, the robustness analysis of the hash image is carried out, and five 512×512 test images Airplane, House, Lena, Baboon and Peppers are selected for various conventional processing, and the robustness attack on each standard image according to Table 1 is obtained 66 The standard image and its 66 similar images form a similar image pair, and the hash Hamming distance of the similar image pair is calculated.
[0094] Table 1: Parameters used for various conventional image processing in the robustness performanc
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap