Repositioning processing method and system
A processing method and relocation technology, applied in the field of relocation, can solve the problems of not supporting encryption algorithms, failure of the relocation process, etc., and achieve the effect of avoiding the failure of the relocation process
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
example 1
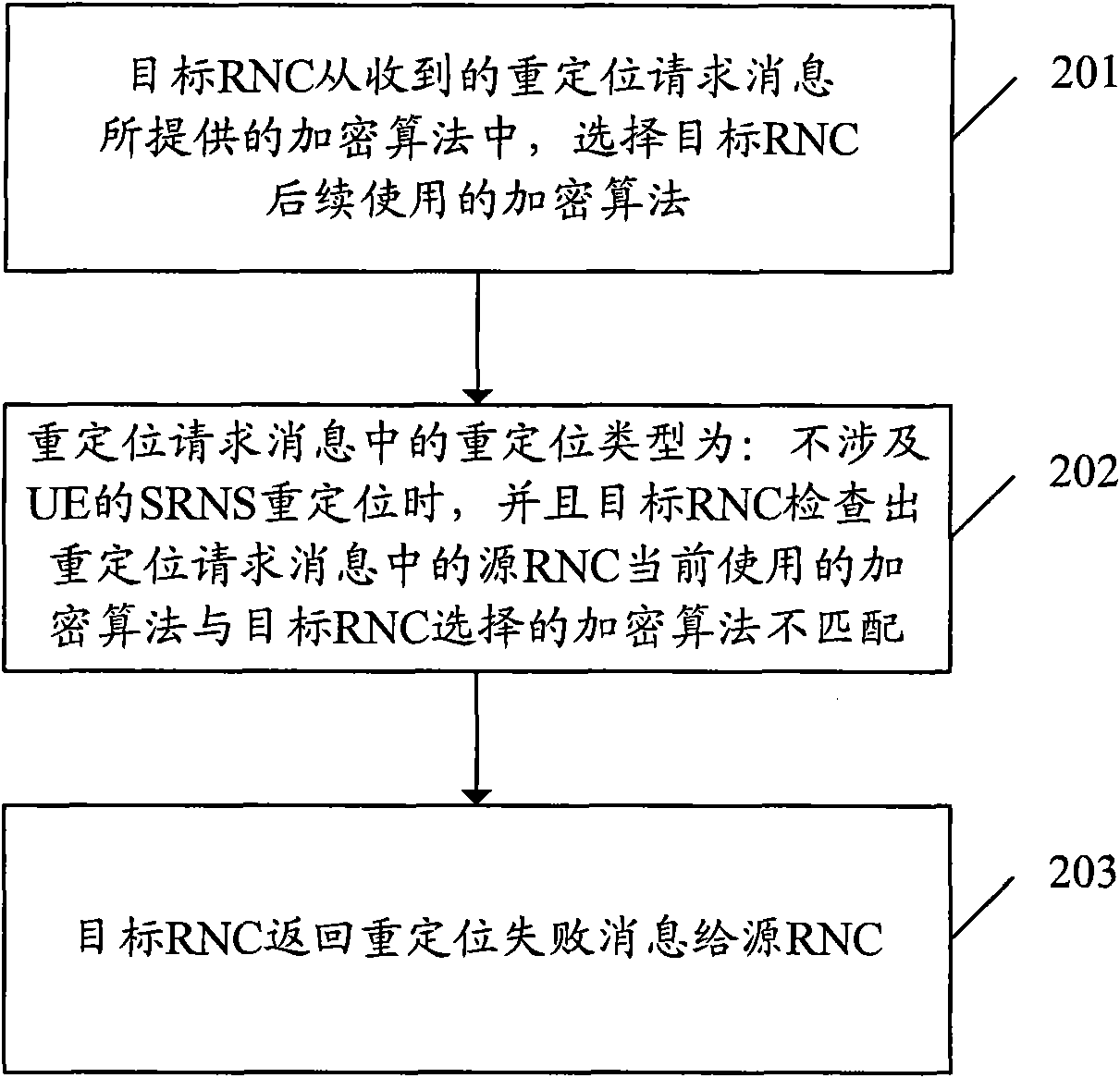
[0063] Example 1: The content carried in the relocation failure message is: the encryption algorithm used by the SRNC is not supported. This example includes the following steps:
[0064] Step 301, the target RNC receives a relocation request message. The message includes a list of preferred integrity protection algorithms and encryption algorithms recommended by the CN. The target RNC must select an available integrity algorithm and encryption algorithm from the integrity protection algorithm list and encryption algorithm list.
[0065] Step 302, the target RNC selects the integrity protection algorithm IA and encryption algorithm EA that the target RNC needs to use according to the integrity protection algorithm capability and encryption algorithm capability supported by itself, as well as the preferred integrity protection algorithm list recommended by the CN, and the preferred data encryption algorithm list .
[0066] Step 303, the target RNC acquires the integrity protect
example 2
[0068] Example 2: The content carried in the relocation failure message is: the encryption algorithm support capability of the target RNC itself. This example includes the following steps:
[0069] Step 401, the target RNC receives a relocation request message. The message includes a list of preferred integrity protection algorithms and encryption algorithms recommended by the CN. The target RNC must select an available integrity algorithm and encryption algorithm from the integrity protection algorithm list and encryption algorithm list.
[0070] Step 402, the target RNC selects the integrity protection algorithm IA and encryption algorithm EA that the target RNC needs to use according to the integrity protection algorithm capabilities and encryption algorithm capabilities supported by itself, as well as the preferred integrity protection algorithm list recommended by the CN, and the preferred data encryption algorithm list .
[0071] Step 403, the target RNC obtains the inte
example 3
[0073] Example 3: The content carried in the relocation failure message is: a list of preferred data encryption algorithms recommended by the CN. This example includes the following steps:
[0074] Step 501, the target RNC receives a relocation request message. The message includes a list of preferred integrity protection algorithms and encryption algorithms recommended by the CN. The target RNC must select an available integrity algorithm and encryption algorithm from the integrity protection algorithm list and encryption algorithm list.
[0075] Step 502, the target RNC selects the integrity protection algorithm IA and encryption algorithm EA that the target RNC needs to use according to the integrity protection algorithm capability and encryption algorithm capability supported by itself, as well as the preferred integrity protection algorithm list recommended by the CN, and the preferred data encryption algorithm list .
[0076] Step 503, the target RNC acquires the integri
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap