Method, device and apparatus for controlling service dedicated line
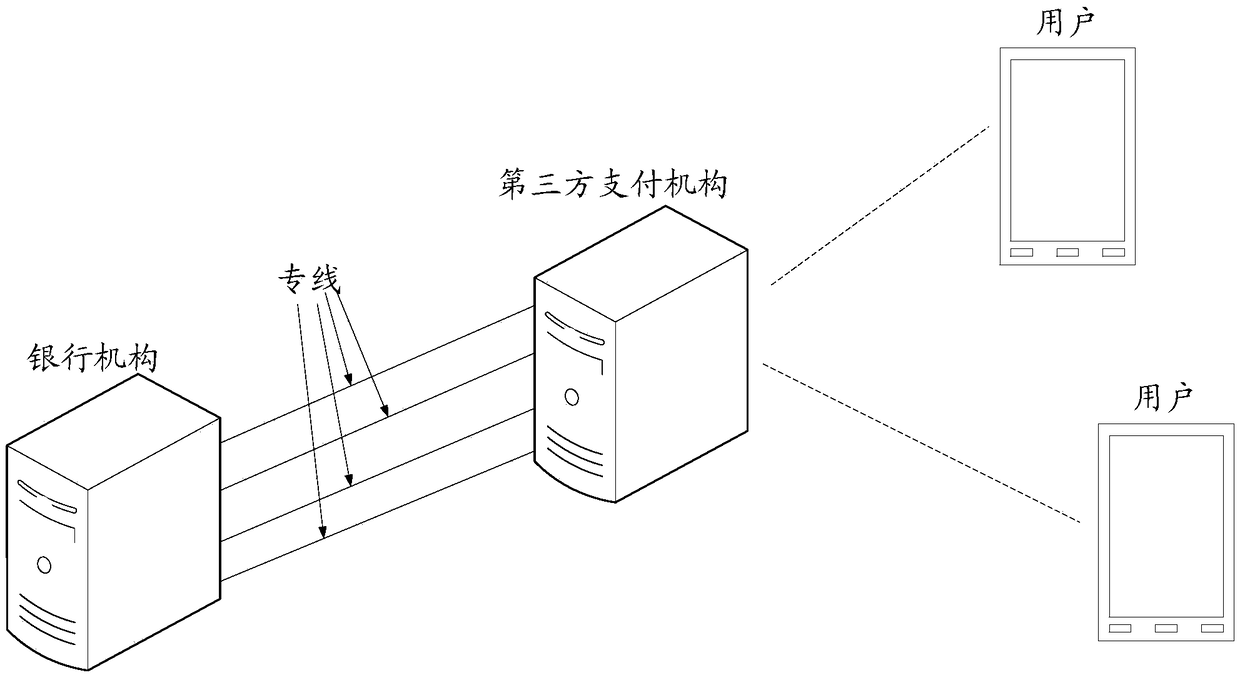
A dedicated line and business technology, applied in the computer field, can solve problems such as network link avalanche effect, third-party payment institution or banking institution abnormality, etc., to reduce the avalanche effect and ensure the efficiency of business processing.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment 1
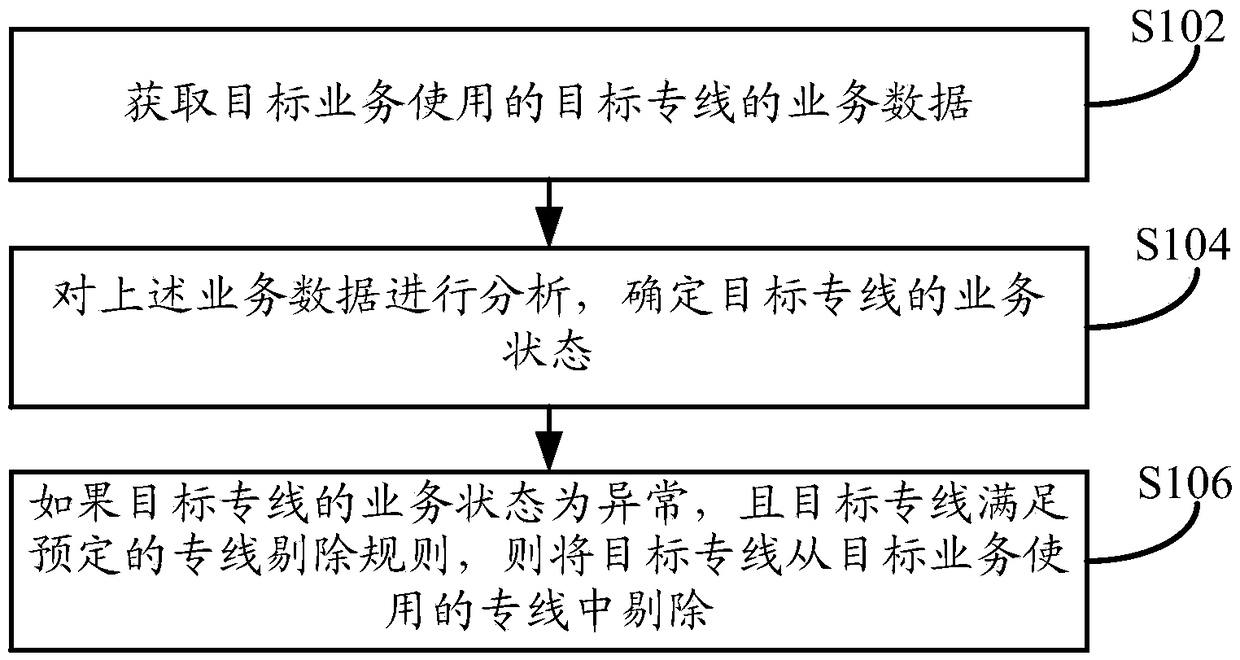
[0074] Such as figure 1 As shown, the embodiment of this specification provides a method for controlling a dedicated service line, and the method may be executed by a terminal device or a server, where the terminal device may be a personal computer or the like. The server can be an independent server, or a server cluster composed of multiple servers, and the server can be a background server of a certain business (such as financial services, etc.), or a website (such as an online shopping website or payment application, etc.) background server, etc. This method can be used to detect and analyze the business status of a dedicated line owned by a certain service, and to eliminate abnormal dedicated lines. The execution subject is a server as an example for illustration. For the case of a terminal device, it can be handled according to the following relevant content, and will not be repeated here. The method specifically may include the following steps:
[0075] In step S102, the
Embodiment 2
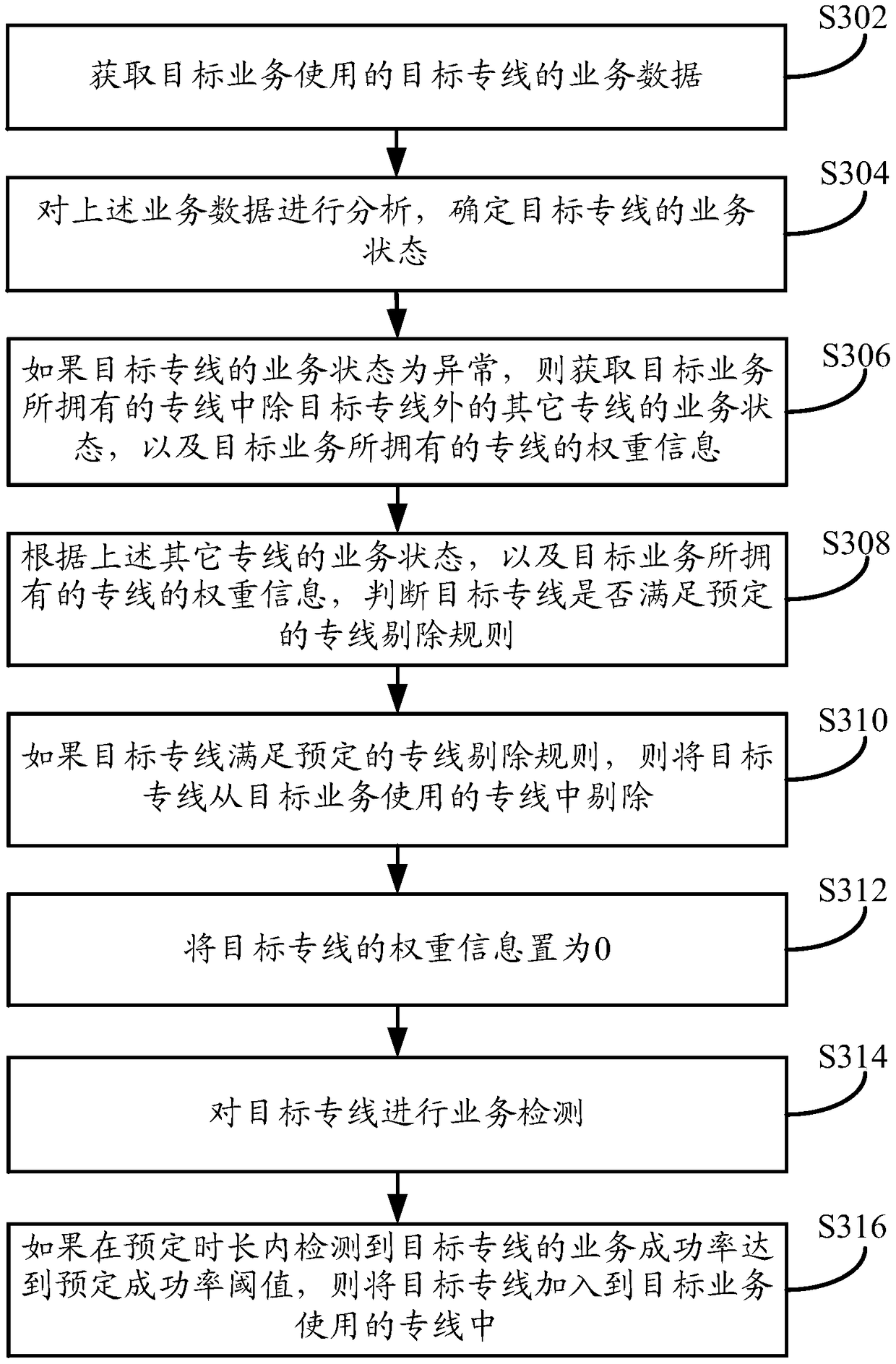
[0089] Such as image 3 As shown, the embodiment of this specification provides a method for controlling a dedicated service line, and the method may be executed by a terminal device or a server, where the terminal device may be a personal computer or the like. The server can be an independent server, or a server cluster composed of multiple servers, and the server can be a background server of a certain business (such as financial services, etc.), or a website (such as an online shopping website or payment application, etc.) background server, etc. This method can be used to detect and analyze the business status of a dedicated line owned by a certain service, and to eliminate abnormal dedicated lines. The execution subject is a server as an example for illustration. For the case of a terminal device, it can be handled according to the following relevant content, and will not be repeated here. The method specifically may include the following steps:
[0090] In step S302, the
Embodiment 3
[0137] Such as Figure 4 As shown, the embodiment of this specification provides a method for controlling a dedicated service line, and the method may be executed by a terminal device or a server, where the terminal device may be a personal computer or the like. The server can be an independent server, or a server cluster composed of multiple servers, and the server can be a background server of a certain business (such as financial services, etc.), or a website (such as an online shopping website or payment application, etc.) background server, etc. This method can be used to detect and analyze the business status of a dedicated line owned by a certain service, and to eliminate abnormal dedicated lines. The execution subject is a server as an example for illustration. For the case of a terminal device, it can be handled according to the following relevant content, and will not be repeated here.
[0138] This embodiment takes the actual application scenario as an example to des
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap