Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
3 results about "Digital storage" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Methods for combating malicious software
A method for combating malware monitors all attempts by any software executing on a computer to write data to the computer's digital storage medium and records details of the attempts in a system database having a causal tree structure. The method also intercepts unauthorized attempts by executing objects to modify the memory allocated to other executing objects or to modify a selected set of protected objects stored on the digital storage medium, and may also intercept write attempts by executing objects that have a buffer overflow or that are executing in a data segment of memory. The method may include a procedure for switching the computer into a quasi-safe mode that disables all non-essential processes. Preferably, the database is automatically organized into software packages classified by malware threat level. Entire or packages or portions thereof may be easily selected and neutralized by a local or remote user.
Owner:ROBOT GENIUS
Digital cueing receiver
ActiveUS7136009B1Low costReduce complexityCommunication jammingRadio wave reradiation/reflectionRadio receiverAnalog delay line
A digital cueing radio receiver system embodied using digital memory in lieu of analog delay lines and thereby avoiding delay line implementation difficulties. The cueing receiver system includes a wideband receiver portion providing an output signal employed for tuning a narrowband receiver portion of the system. Signal delay enabling use of the wideband receiver portion output signals for tuning the narrow band receiver portion selection frequency is provided by a digital memory circuit operating on analog-to-digital converted samples of input signal data of the receiver system. Approximated unity value related mathematical multiplication free Kernel function values are employed in the Fourier transformation. Avoidance of analog delay line-elements in embodying the system is a significant practical advantage of the invention.
Owner:AIR FORCE THE UNITED STATES AS REPRESENTED BY THE SEC OF THE
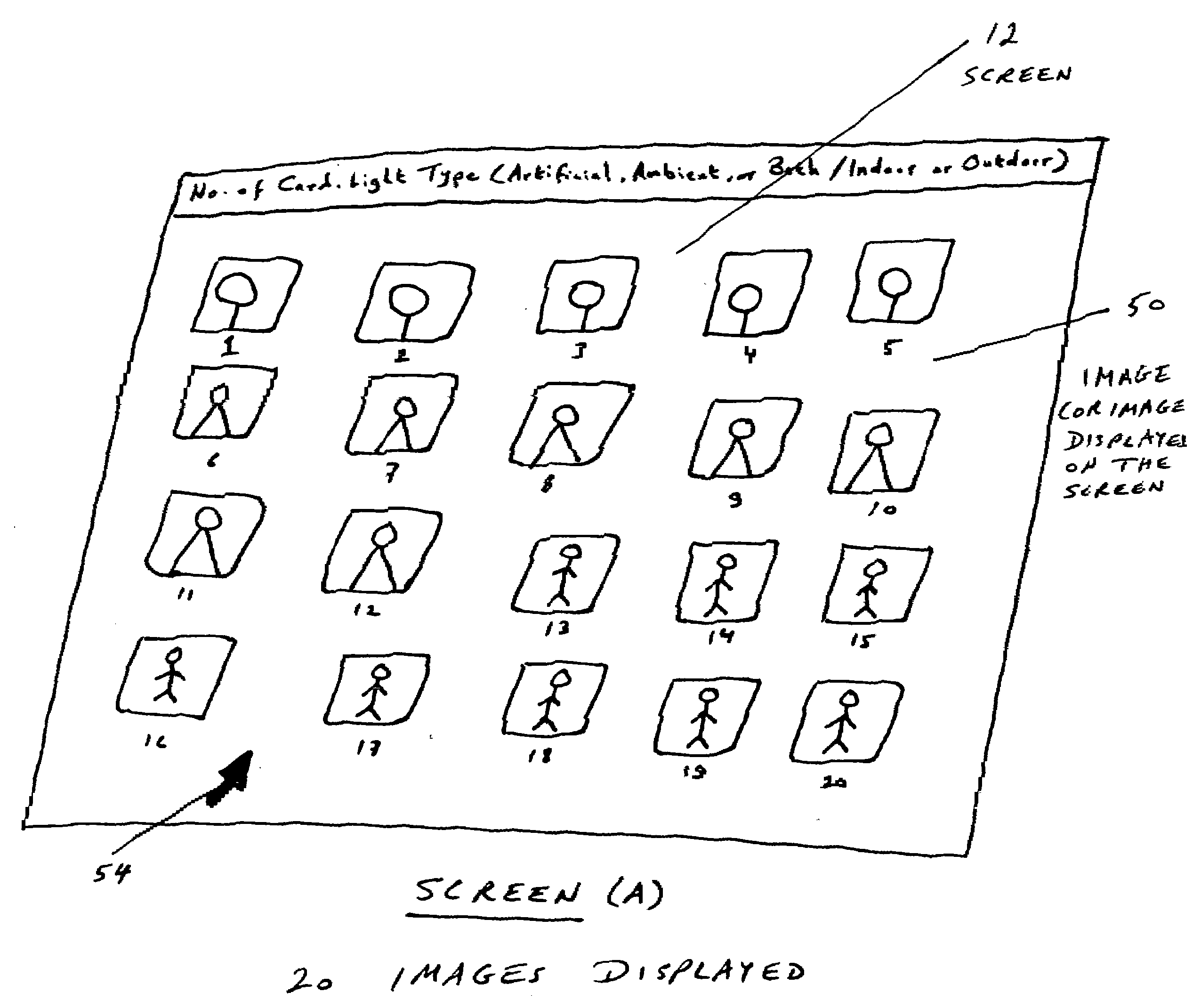
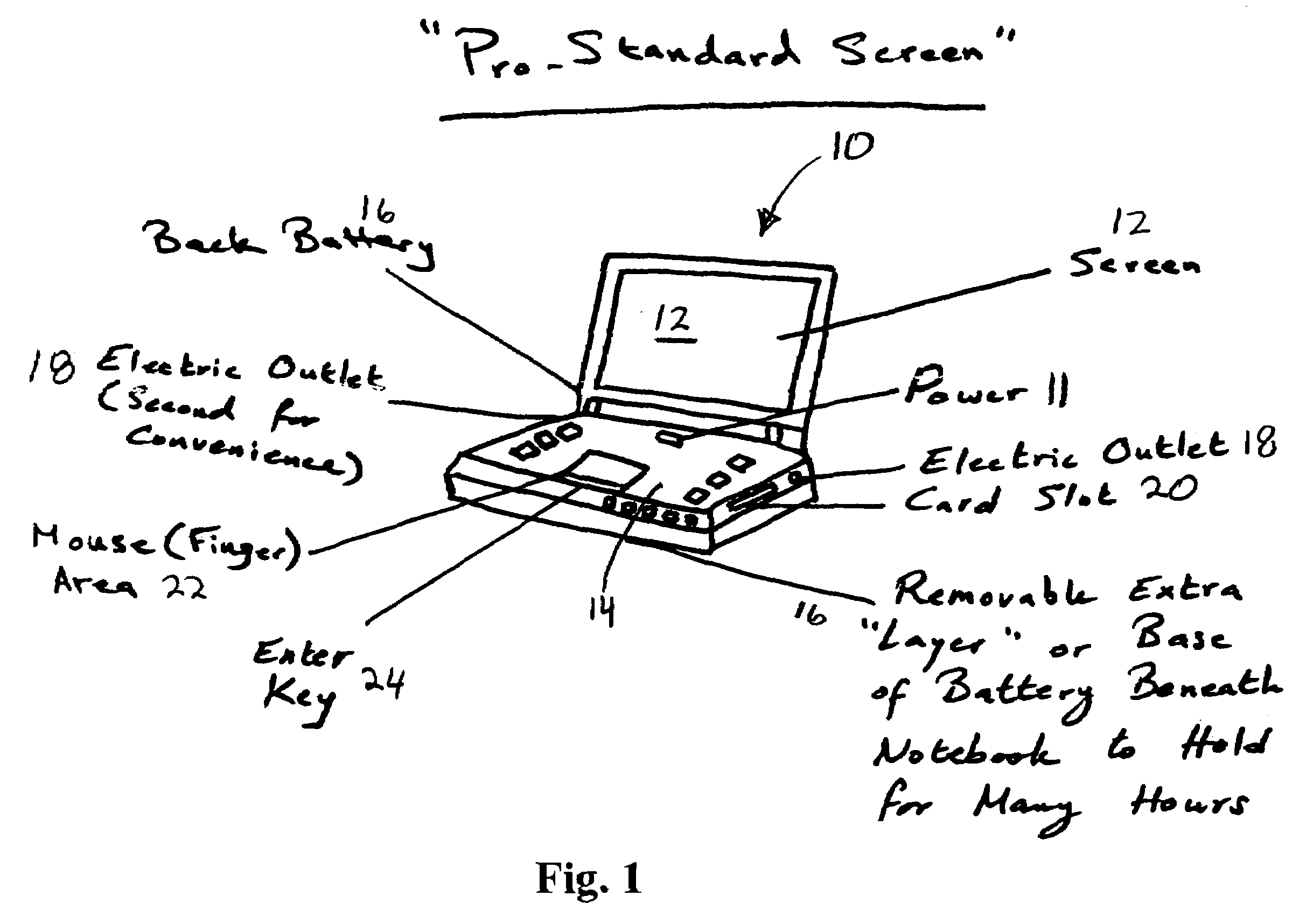
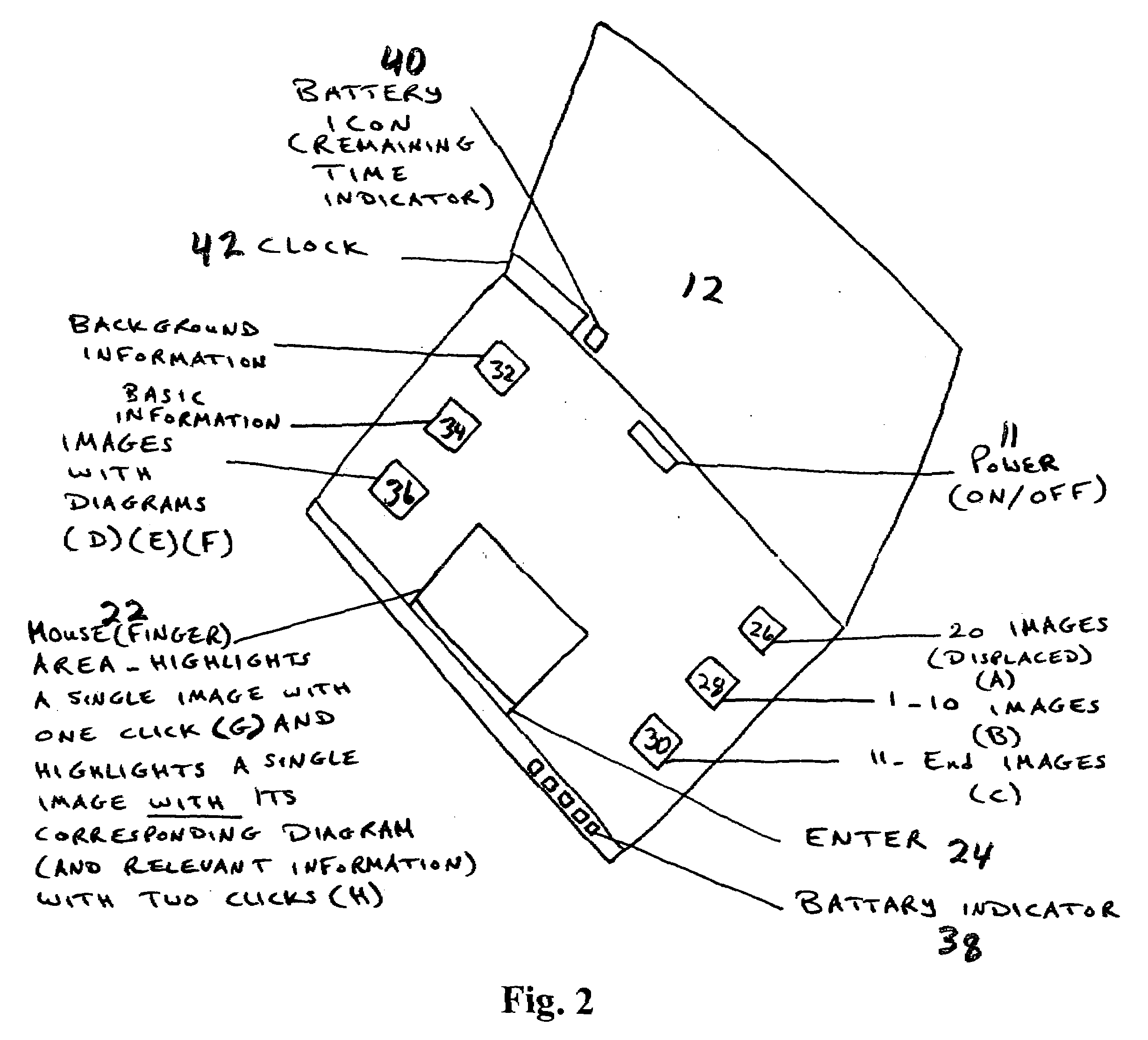
Comparison apparatus and method for obtaining photographic effects
InactiveUS20080036894A1Television system detailsColor television detailsCamera lensRelevant information
Owner:ALSAUD MOHAMMED
Popular searches
Who we serve
- R&D Engineer
- R&D Manager
- IP Professional
Why Eureka
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Social media
Try Eureka
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap