Network attack determination method and system, electronic equipment and storage medium
A technology for network attack and determination method, applied in the field of network security, can solve the problems of loopholes in defense measures, massive data analysis, missed network attack events, etc., to achieve the effect of improving network security level and rapid detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment 1
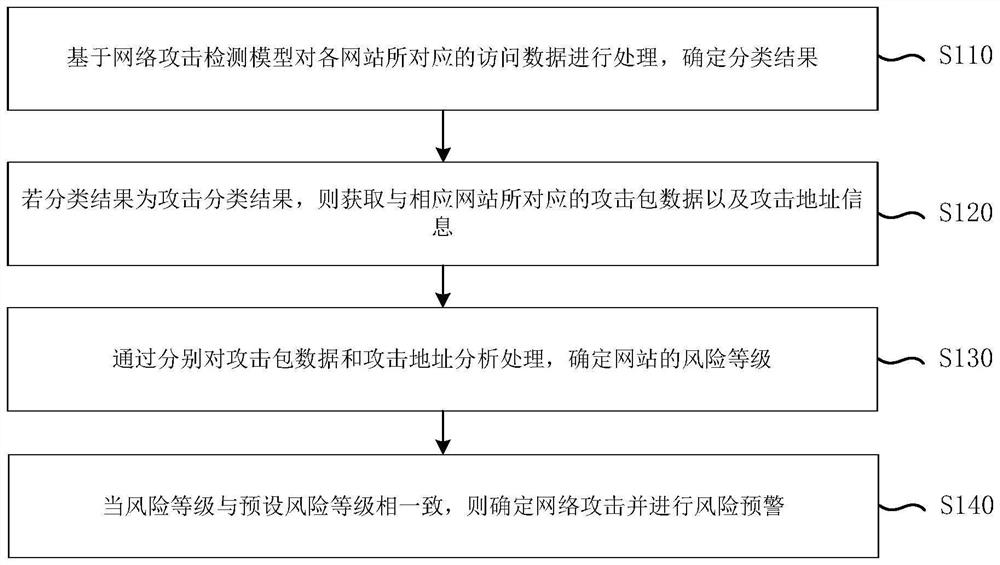
[0028] figure 1 A flowchart of a method for determining a network attack provided in Embodiment 1 of the present invention. This embodiment can be applied to the situation of determining whether there is a network attack. The method can be executed by the system for determining a network attack in the embodiment of the present invention. The apparatus may be implemented by means of software and / or hardware, and optionally, may be implemented by an electronic device, and the electronic device may be a PC terminal or a server terminal or the like. The apparatus may be configured in a computing device, and the method for determining a network attack provided by this embodiment specifically includes the following steps:
[0029] S110. Process the access data corresponding to each website based on the network attack detection model, and determine a classification result.
[0030] The network attack detection model may be a detection model generated based on historical attack record
Embodiment 2
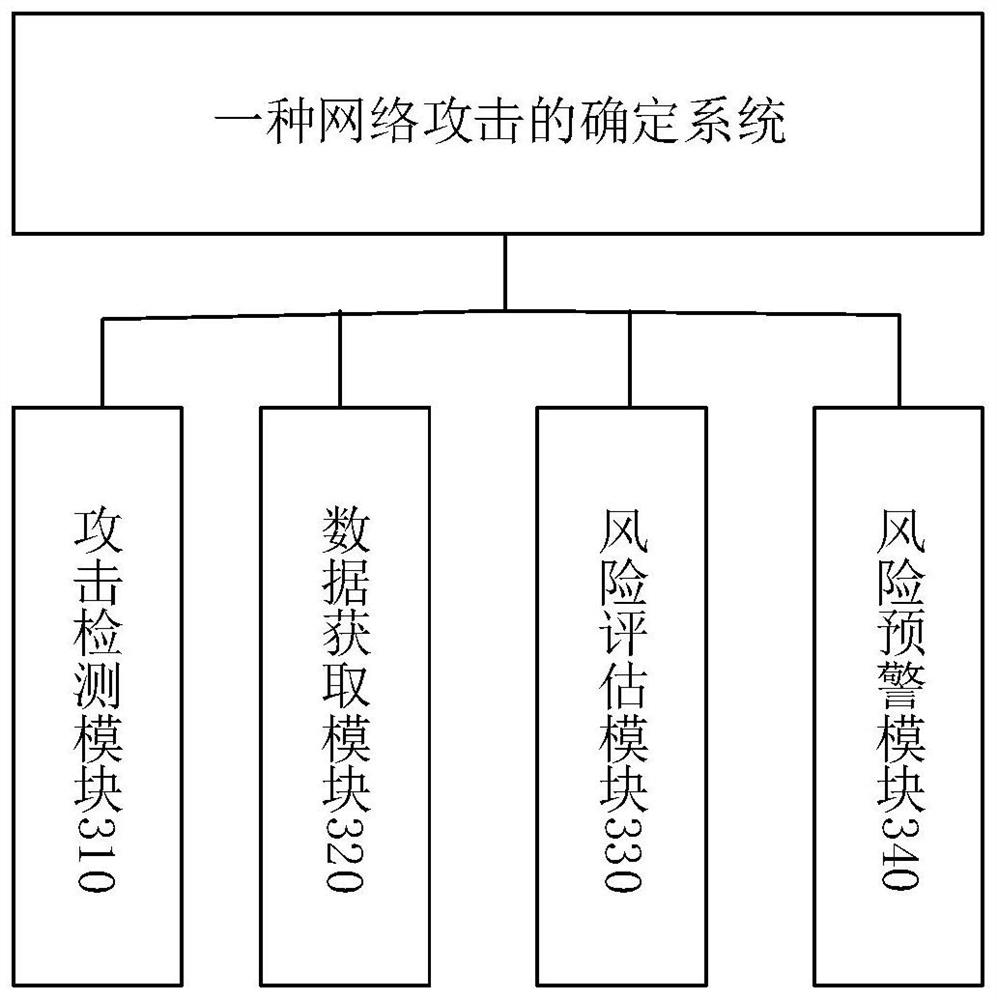
[0069] image 3This is a structural block diagram of a system for determining a network attack provided by Embodiment 2 of the present invention. The device includes: an attack detection module 310 , a data acquisition module 320 , a risk assessment module 330 , and a risk early warning module 340 .
[0070] The attack detection module is used to process the access data corresponding to each website based on the network attack detection model to determine the classification result;
[0071] a data acquisition module, configured to acquire attack packet data and attack address information corresponding to the corresponding website if the classification result is an attack classification result;
[0072] The risk assessment module is used to determine the risk level of the website by analyzing and processing the attack packet data and the attack address respectively;
[0073] The risk early warning module is used to determine the network attack and carry out risk early warning wh
Embodiment 3
[0093] Figure 4 This is a schematic structural diagram of an electronic device according to Embodiment 3 of the present invention. Figure 4 A block diagram of an exemplary electronic device 40 suitable for use in implementing embodiments of the present invention is shown. Figure 4 The electronic device 40 shown is only an example, and should not impose any limitation on the function and scope of use of the embodiments of the present invention.
[0094] like Figure 4 As shown, the electronic device 40 takes the form of a general-purpose computing device. Components of electronic device 40 may include, but are not limited to, one or more processors or processing units 401, system memory 402, and a bus 403 connecting different system components (including system memory 402 and processing unit 401).
[0095] Bus 403 represents one or more of several types of bus structures, including a memory bus or memory controller, a peripheral bus, a graphics acceleration port, a processor
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap