Method and system for third party application interface authorization
An application interface, third-party technology, applied in the field of Internet security, can solve single problems and achieve the effect of improving network security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0038] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments.
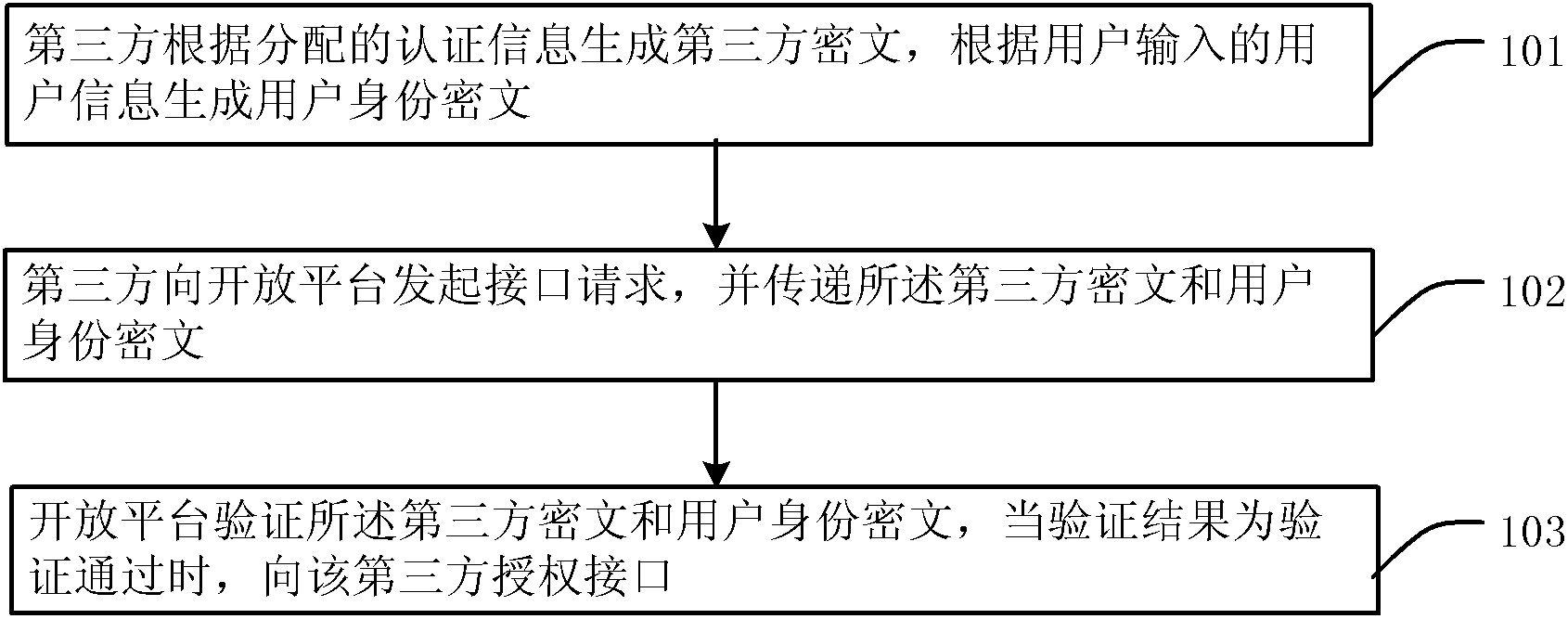
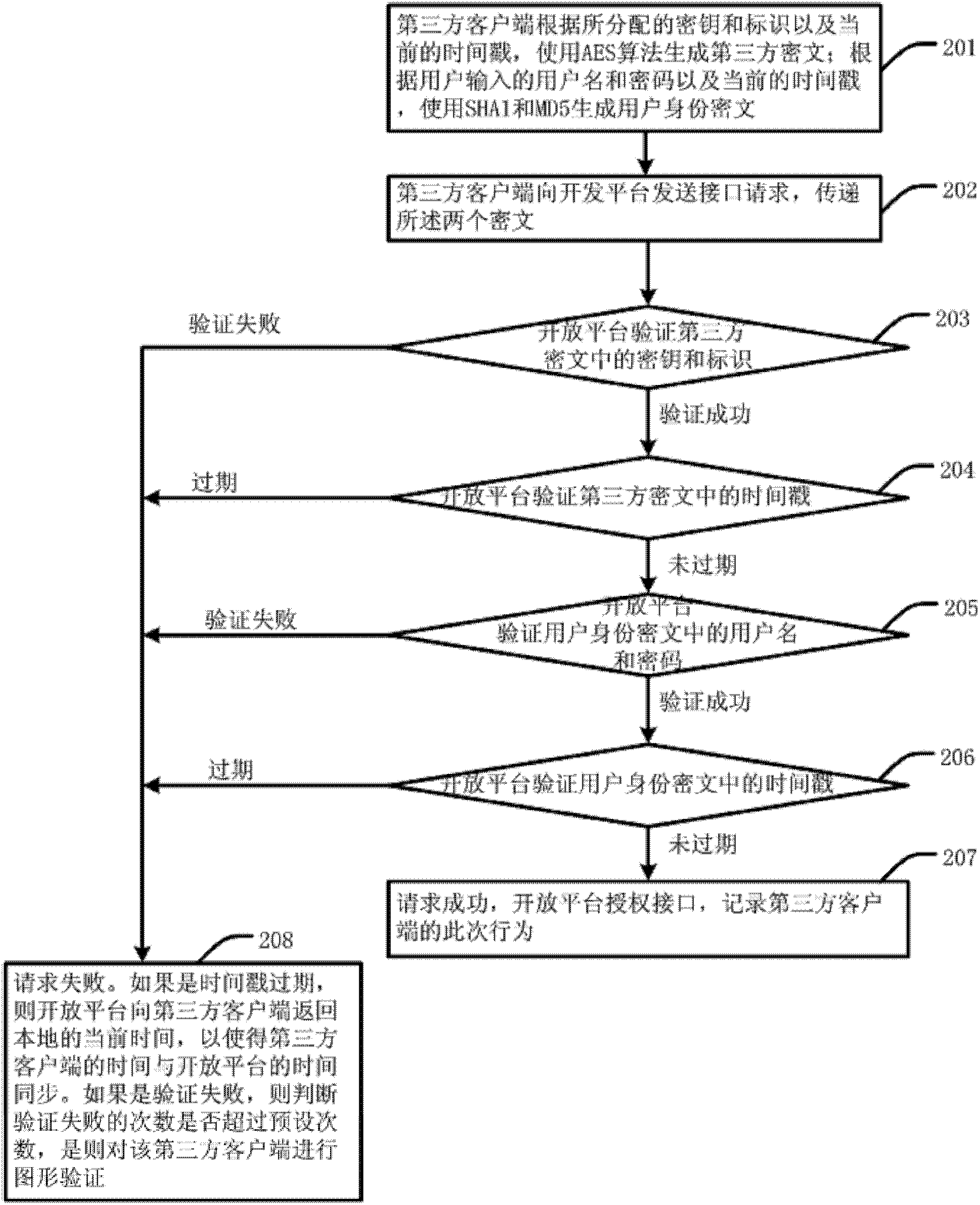
[0039] figure 1 It is a flowchart of a method for authorizing a third-party application interface in an embodiment of the present invention. Such as figure 1 As shown, the method includes:
[0040] 101. The third party generates a third-party ciphertext according to the assigned authentication information, and generates a user identity ciphertext according to the user information input by the user.
[0041] In this step, the authentication information includes: key and identification information; the third party uses the Advanced Encryption Standard (AES) algorithm to generate third-party ciphertext according to the key and identification. The user information includes: user name and password; the third party uses the first version of the secure h
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap